Cyber Security Support Options for Small Businesses
Every year, thousands of small businesses are victims of cyber security breaches. In fact, according to Verizon’s 2021 Data Breach Investigation Report, 46% of these attacks targeted companies with less than 1,000 employees.
In this article, we explore why cyber security is important and the support options that are available for small businesses.
Why cyber security matters for small businesses
Small businesses are particularly vulnerable to a number of cyber attacks, including brute force attacks, malware, ransomware, and social attacks.
Unfortunately, many small businesses don’t survive even a single attack. The average cost of a data breach for companies with fewer than 500 employees is $2.98 million, according to a survey by IBM and the Ponemon Institute. Recovery expenses alone force most of these small businesses to close within six months of the attack.
Cyber security challenges for small businesses
With limited resources, small businesses often struggle to secure their networks, data, and systems from potential cyber threats.
Common cyber security challenges for small businesses include:
- A lack of awareness and understanding of the importance of cyber security.
- Limited resources to support it.
- A lack of expertise in the area.
- Difficulty implementing appropriate technical controls.
- Difficulty staying up-to-date on current threats.
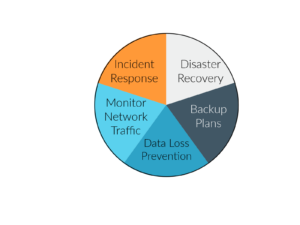
Areas of cyber security that need support coverage
The domain of cyber security is large and it covers a number of practice areas that require specialized skillsets and knowledge. Some of the most visible areas of cyber security requiring consistent support include:
- Incident Response – This includes the creation of policies and procedures to identify, stop, and eliminate cyberattacks.
- Monitor Network Traffic – An outside firm can ideally monitor all traffic for malicious activity, including possible hacks and data breaches.
- Data Loss Prevention – Data can be lost in many ways other than just a cyber attack. This service creates plans and procedures for avoiding losses before they happen.
- System Backups and Disaster Recovery – Raging from an earthquake or hurricane to full-scale cyber attack, disaster recovery is a specialty that requires a team that understands how to put everything back together quickly.
Support options available for small businesses
There are different levels of cybersecurity support available depending on the scope of services needed (i.e., partial support vs. full support), budget limitations, and scale. Services will generally be delivered under one of two models:
- Managed (cyber security) services –
- Managed security services providers (MSSPs) employ a team of experts who actively monitor networks, manage security infrastructure, and respond to incidents promptly
- Emphasis is on prevention, detection, and mitigation of cyber threats to maintain a secure environment
- Scope (what areas of support are needed), scale, SLA, and pricing will be tailored to your organization’s needs
- Example: 24/7 security monitoring, vulnerability management, threat intelligence, incident response, and device patching services
- Advisory / Consulting / Custom Engagements
- Custom support and pricing based on a specific project-based need
- Example: perform a security gap analysis and provide a comprehensive remediation report
- Can be provided by agencies or independent consultants
Types of managed cyber security solutions
Within the managed security services model, small businesses can choose from either full-support or partial support, depending on needs, priorities, and resource limitations.
- Partial support – A team will manage only a subset of one or more areas of your cybersecurity program based on your needs and priorities For example, you might want a team to track changes and vulnerabilities within your servers while you handle email security separately.
- Full support – This is comprehensive, all-inclusive cyber security covering all relevant dimensions of your cybersecurity program. A team will monitor your entire system and continuously identify and address security vulnerabilities and active security threats.
Services covered under managed security service models
Whether you choose partial or full support, there are specific areas where your support team will focus. Common areas covered by managed security services include:
- Threat management solutions help businesses identify and mitigate potential threats before they become problems.
- Managed detection and response services offer active monitoring to ensure that malicious cyber activity is addressed quickly.
- Managed cloud security helps to protect data stored in the cloud.
- Managed endpoint security protects against unauthorized access to critical systems.
- Managed identity solutions protect user identities from being stolen or abused online.
- A security command center provides real-time insights into an organization’s cyber landscape.
Types of cyber security consulting and advisory services
Where managed security solutions cover ongoing/recurring cyber security activities, consulting engagements primarily focus on discreet, individual projects and specialized requests.
Projects will be tailored to each organization’s unique circumstances, but typical examples of security consulting engagements include:
- On-demand security expertise – A model where organizations have on-demand access to security experts, when needed.
- Security operations gap assessment – A one-time assessment of an organization’s current security operations (personnel, procedures, policies, etc.).
- Security compliance roadmap development – Creation of an action plan for an organization to achieve and sustain compliance according to a given security standard, framework, or custom set of requirements.
- Cyber security insurance advisory – Helping organizations assess and optimize the balance of risk insurance relative to their overall risk profile and threat response capabilities.
- Risk and security posture assessment – A one-time assessment to help organizations understand and evaluate their overall security risks
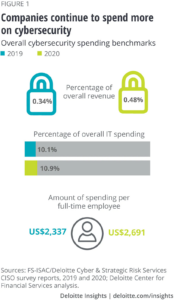
Costs of cyber security support for small businesses
According to a 2020 survey by Deloitte, respondents spent about 10.9% of their IT budget on cybersecurity, or about $2,700 per full-time employee. Today, small businesses seeking cybersecurity support must consider the cost-benefit tradeoffs between full or partial support.
Partial support costs
Partial support services often focus on the most critical areas of cybersecurity that may be too costly, time-intensive, or technically complex for internal resources to manage, such as:
- Risk assessments
- Firewall operations
- Breach monitoring and remediation
- Endpoint security
- Endpoint detection and response (EDR)
Support costs for partial coverage will vary depending on the scope and scale of the services needed. For example, email security may fall between $3 and $6 per user per month, whereas firewall support may include one-time setup fees from $1,500-$15,000 plus monthly maintenance fees of $10-$500, depending on network size.
Ultimately, budget strapped organizations often struggle to find the right balance of cost and service coverage. In these instances, it is best to first determine an organization’s overall risk profile through an externally managed risk assessment to help identify security priorities.
Full support costs
As with partial support, full support costs may also vary depending on several factors, such as:
- A company’s size and industry
- Regulation and compliance requirements that affect your business
- Sensitivity of the information you gather, use, and distribute
- Requests from clients or stakeholders in the company
- The complexity of cyber network
By some estimates, full cybersecurity support for SMB’s may range from $2,500 to $2,800 per year per full-time employee or $200 – $233 per month per employee.
However, costs for companies that deal with highly complex or sensitive data (e.g., brokerage firms, healthcare organizations, law firms, etc.) can be much higher.
Costs of doing nothing
Some organizations may overlook cybersecurity as a critical business function, assuming the risks may be minimal for their business or industry.
With cybercrime on the rise, however, organizations that fail to mitigate cyber risk are often the most vulnerable. While not investing in cybersecurity may sound like a cost-saving strategy, one should also consider that the cost of a cyber attack averages between $120,000 and $1.24 million, and most attacked companies are out of business within six months.
Consulting and one-time project costs
With hourly rates and project sizes varying, budgeting for a new project may be hard to predict. However, assuming cyber security consultant labor rates average between $75-$200 USD/hr, one could roughly expect security consulting projects to fall within one of the following categories:
- Small projects/engagements: 20-120 hours ($1.5K – $24K)
- Medium projects: 120-399 hours ($9K – $79.8K)
- Large projects: > 400 hours $30K-$80K+)
How to find cyber security support
Terms to search for
Consider using one of the following terms or titles when searching for security support solutions, depending on your specific needs:
If searching for consultants:
- Fractional CTO (Chief Technology Officer) – A part-time C-level, technical executive that covers the functions of a Chief Technology Officer in lieu of a full-time CTO.
- vCISO (Virtual Chief Information Security Officer) – Similar to a fractional CTO, but focuses more narrowly on the areas of cyber security and information security.
- Cyber/information/computer/database/network security consultant – Any security-focused consultant specializing in one of many subcategories of “cyber” security.
If searching for agencies or larger solution providers:
- Managed security services provider (MSSP) – A security-focused agency that provides external monitoring and management of devices and systems.
- Security-as-a-Service – A business model where a security provider provides security services to customers on a subscription basis.
- Managed Detection and Response (MDR) – A sub-category of security-as-a-service that focuses on the detection and response to security threats, especially network threats.
- Managed SIEM – Also known as SIEM as a service, whereby an MSSP offers security information and event management as a service.
- SOC-as-a-Service or vSOC – An outsourced solution where security analysts provide around-the-clock monitoring of a network and respond to emerging threats.
Where to look
Cybersecurity-focused membership organizations
If you’re looking for a long-term, community-recognized professional, consider exploring a cybersecurity membership organization, such as the Information Systems Security Association International (ISSA). Such membership organizations are dedicated to the development of information systems and security professionals.
Professional job boards and job/resume aggregators
General job boards and job aggregators offer large and diverse talent pools from which to choose. Some of the most popular job boards include:
Specialized job boards and job aggregators
In addition to large job boards, consider exploring specialized job boards that focus on cybersecurity and Information Technology, such as:
Recruiters
IT and cybersecurity-focused recruiters such as these can help organizations identify and screen the best candidates for an organization’s needs:
Freelancing sites
Freelancing sites like Fiverr and Upwork make it relatively easy to hire freelance consultants for small and medium-sized engagements.
Talk to Ihloom
If you’re still struggling to find external support that works for your organization, talk to Ihloom. From a la carte consulting to full-coverage managed services and compliance management, Ihloom specializes in security solutions for small and medium-sized organizations.
How to choose support
How do you choose the right support option for your organization? Here are some general guidelines to help simplify the selection process:
1. Understand your security needs, risk, and vulnerabilities — First, identify the areas where you need assistance. This will help narrow down the potential providers. Also consider the type of data you need to protect, where your users are located, and how accessible their systems should be. If you’re unsure where you need coverage, you can perform your own cyber security assessment or hire a professional.
2. Specify your budget — Second, establish your annual and monthly budget for cybersecurity services. This information will help contractors and solution providers concentrate their efforts on the most important aspects of your security.
3. Identity must-have qualifications — If security needs and budget limitations are still compatible, start making a list of the must-have qualifications and capabilities of your support team. In addition to supporting you in areas where it is needed and within your budget, you may want to also consider other qualifications, such as:
- What certifications do they have?
- How long have they been established?
- Are they reliable?
- Have they won awards or been featured in articles or lists?
- What kind of user reviews do they have?
If you’re looking for a support team that is easy to talk to directly, pay special attention to your initial conversations. Do they understand your business and concerns? Are they able to guide you through the process?
Ihloom Services and Solutions for Small Businesses
Ihloom, of Needham, MA, is a cyber security consultancy designed specifically for small- to medium-sized businesses.
- Managed services – Comprehensive, managed solutions for cybersecurity and compliance certification programs with services including:
- Risk assessments
- Vulnerability audits, remediation, monitoring
- Breach monitoring, remediation
- Endpoint management, detection, response
- Security awareness training
- Patch automation, policy enforcement
- Hardware and Software inventory discovery
- System/data backups
- Security and audit preparation services
- Industry consulting – Reliable access to cyber security and compliance expertise and common challenges, such as:
- Cyber security insurance advisory
- Cyber security compliance advisory
- Cyber security risk consulting
- Cyber security operations consulting
- Custom engagements – Customized solutions for unique challenges, one-off projects, a mixture of services and consulting hours, etc.








0 Comments